9 Open Source Cloud Security Tools You Need in 2026
9 Open Source Cloud Security Tools You Need in 2026
The State of Cloud Security in 2026: Why Testing Tools Matter More Than Ever
Here are the top open source cloud security testing tools covered in this article:
| Tool | Primary Use | Supported Clouds |
|---|---|---|
| Prowler | Compliance auditing & posture management | AWS, Azure, GCP, Kubernetes |
| Trivy | Container, IaC & Kubernetes scanning | AWS, Azure, GCP |
| CloudSploit | Misconfiguration detection | AWS, Azure, GCP, OCI |
| CloudMapper | Network visualization & IAM mapping | AWS |
| OSSEC | Host-based intrusion detection | Multi-cloud workloads |
| OpenVAS | Vulnerability management | Multi-cloud |
| Kubescape | Kubernetes hardening | Kubernetes, cloud-native |
| Pacu | AWS penetration testing | AWS |
| Nikto | Web server & API security testing | Cloud-hosted apps |
Cloud environments move fast. Resources spin up and disappear in seconds. APIs connect everything. And misconfigurations — not sophisticated hacks — are the root cause of most breaches.
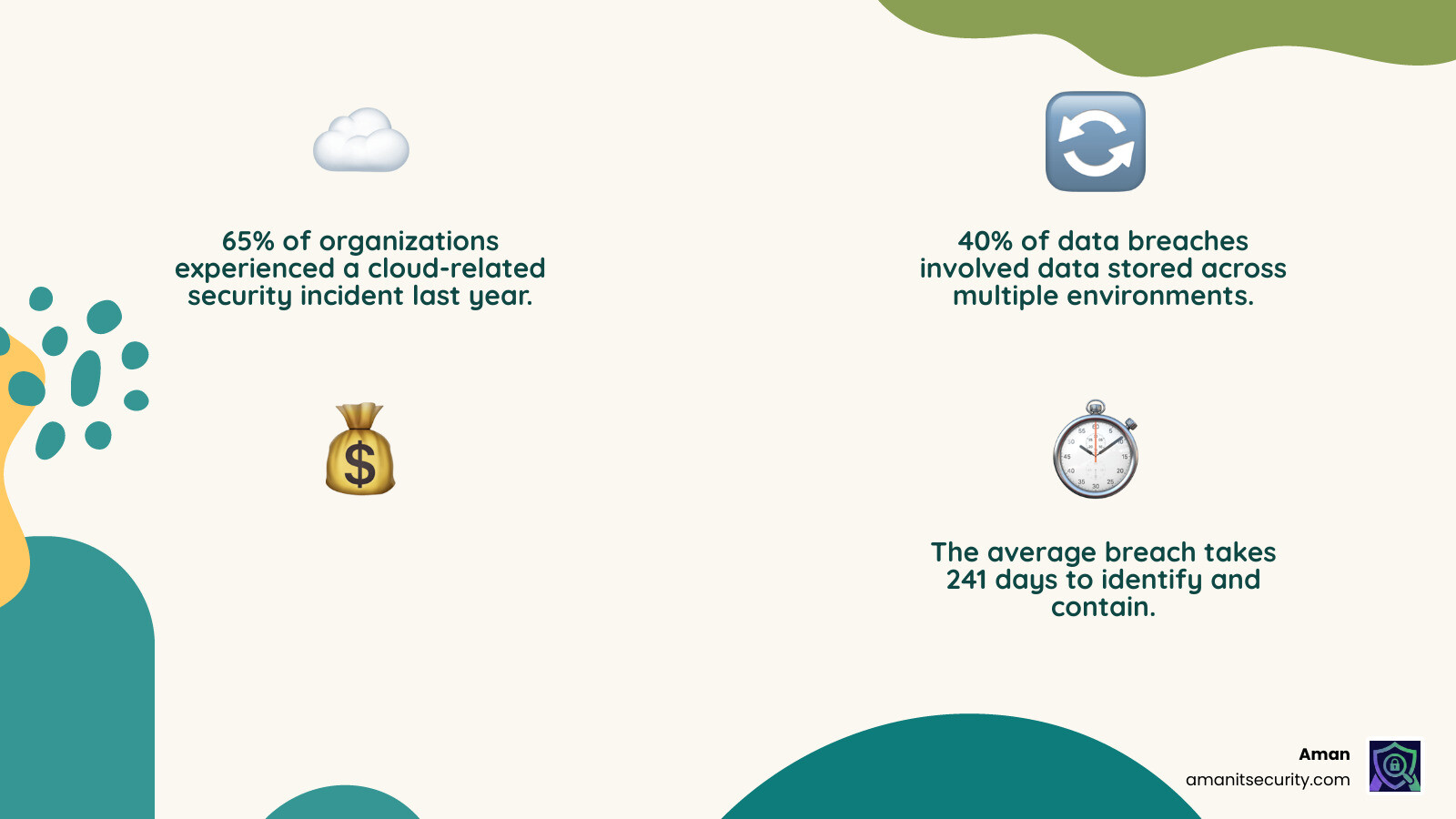
The numbers tell a stark story:
- 65% of organizations experienced a cloud-related security incident last year
- 40% of data breaches involved data stored across multiple environments
- Public cloud storage breaches cost an average of $5.17 million per incident
- The average breach takes 241 days to identify and contain
Yet 89% of enterprises now run in multi-cloud environments, where visibility gaps multiply and manual security reviews simply cannot keep pace.
The good news? A new generation of open source cloud security testing tools gives security teams — even lean ones — powerful, automated ways to find and fix risks before attackers do. And most of them are completely free.
I’m Zezo Hafez, an AWS and Azure certified cloud architect with over 15 years of experience in web development and cloud infrastructure, and I’ve spent considerable time evaluating and implementing cloud security testing tools across single, multi, and hybrid cloud environments. In the sections below, I’ll walk you through the nine open source tools that deliver the most value for real-world cloud security in 2026.
Why Modern Organizations Need Cloud Security Testing Tools
In the “old days” of on-premises data centers, security was like a castle with a moat. You built a strong perimeter and assumed everything inside was safe. But in 2026, the castle has no walls.
Modern organizations rely on ephemeral resources—containers, serverless functions, and auto-scaled virtual machines that might only exist for a few minutes. If you are only running a security scan once a quarter, you are missing the vast majority of your infrastructure’s lifecycle.
According to IBM’s Cost of Data Breach report, breaches related to public cloud storage incur the highest average costs. This is why automated cloud security testing tools are no longer optional. They provide the real-time monitoring and AI-powered threat detection needed to manage multi-cloud sprawl. Without them, you are essentially flying blind in a storm.
By using these tools, we can implement a continuous Infrastructure Scanning Guide Risk Mitigation strategy. This ensures that every time a developer pushes code or an automated script changes a configuration, the environment is immediately checked for “toxic combinations” of risk—like an exposed database paired with a highly privileged identity.
How cloud security testing tools differ from traditional security
Traditional on-premises security tools were designed for static environments. They focused on IP addresses and physical firewalls. But cloud security is different because the “perimeter” is now the Identity and Access Management (IAM) layer.
- Dynamic Scaling: Cloud tools must handle assets that appear and vanish instantly. Traditional scanners often choke on these “ghost” assets.
- Control Plane Risks: In the cloud, an attacker doesn’t just hack a server; they hack the account. If they get hold of your cloud provider’s API keys, they can delete your entire company in seconds.
- Identity-Centric: Security in 2026 is about who can do what to which resource. Traditional tools don’t understand complex IAM relationships.
- Shared Responsibility: You are responsible for securing your data and configurations, while the provider (AWS, Azure, GCP) secures the physical hardware. Cloud security testing tools help you fulfill your end of the bargain.
The role of CNAPP as a holistic platform
As cloud environments grew more complex, we saw the rise of the Cloud-Native Application Protection Platform (CNAPP). Think of CNAPP as the “Swiss Army Knife” of cloud security. It integrates several different categories of cloud security testing tools into one unified view:
- CSPM (Cloud Security Posture Management): Checks for misconfigurations (like an open S3 bucket).
- CWPP (Cloud Workload Protection Platform): Protects the actual “guts” of your apps, like containers and VMs.
- CIEM (Cloud Infrastructure Entitlement Management): Manages permissions to ensure the “principle of least privilege.”
- CASB (Cloud Access Security Broker): Acts as a gatekeeper between your users and your cloud apps.
A CNAPP approach provides unified visibility, ensuring that security isn’t just a series of disconnected alerts, but a cohesive defense strategy.
9 Essential Open Source Cloud Security Testing Tools
Open source tools are the backbone of the security community. They allow us to audit our infrastructure without being locked into expensive, proprietary contracts. Here are the nine heavy hitters you should be using in 2026.
Prowler: The gold standard for cloud security testing tools
If we had to pick just one tool to start with, it would be Prowler. Originally built for AWS, it has expanded to support Azure, GCP, and Kubernetes. Prowler is an open-source security auditing tool that checks your infrastructure against over 250 controls based on the CIS Benchmarks and other regulatory frameworks.
It is incredibly easy to use. You can run it from your terminal or integrate it into a CI/CD pipeline. It generates beautiful reports in HTML, JSON, or CSV, making it a favorite for compliance officers who need to prove they are meeting NIST or ISO 27001 standards.
Trivy: Versatile scanning for containers and IaC
Developed by Aqua Security, Trivy is a versatile security scanner that has become the industry standard for container security. It doesn’t just look for vulnerabilities in your software packages; it also scans your Infrastructure-as-Code (IaC) files (like Terraform or CloudFormation) and Kubernetes configurations.
According to the Greenbone Notable Open Source Cloud Computing Security Tools guide, Trivy’s strength lies in its speed and accuracy. It can detect vulnerabilities in OS packages and language-specific dependencies (like Python, Go, or Java) in seconds, making it perfect for “shifting left” in the development lifecycle.
CloudSploit: Detecting misconfigurations across multi-cloud
CloudSploit is another fantastic tool from the Aqua Security family. It focuses on “agentless” scanning, meaning you don’t have to install any software on your servers. Instead, it connects via API to your cloud provider and scans for security risks.
It supports a wide array of environments, including AWS, Azure, GCP, and even Oracle Cloud (OCI). We love it because it comes with built-in compliance maps for HIPAA and PCI DSS, helping you spot “low-hanging fruit” misconfigurations that could lead to a massive data breach.
CloudMapper: Visualizing AWS network exposure
Sometimes, you just need to see what your network looks like. CloudMapper was originally designed to generate network diagrams for AWS environments. However, it has evolved into a powerful security tool that can identify orphan resources and map out IAM relationships.
By visualizing your network, you can quickly spot resources that are accidentally exposed to the public internet. It’s much easier to see a red line connecting a database to the world on a map than it is to find that same error in a thousand lines of configuration code.
OSSEC: Host-based intrusion detection for cloud workloads
While many cloud security testing tools focus on the “outside” of the cloud, OSSEC focuses on the “inside.” It is a host-based intrusion detection system (HIDS) that monitors your cloud workloads in real-time.
OSSEC performs log monitoring, file integrity checking, and rootkit detection. If an attacker manages to gain access to one of your virtual machines, OSSEC is the “smoke detector” that will alert you to their presence. It even supports “active response,” meaning it can automatically block an IP address if it detects a brute-force attack.
OpenVAS: Comprehensive vulnerability management
OpenVAS (Open Vulnerability Assessment System) has been a staple in the security world since 2006. It is a full-featured vulnerability scanner that performs both unauthenticated and authenticated testing.
In a cloud environment, OpenVAS is excellent for network discovery and scanning your public-facing assets for known vulnerabilities. It is maintained by Greenbone and features a massive, regularly updated feed of vulnerability signatures.
Kubescape: Hardening Kubernetes environments
Kubernetes is the engine behind most cloud-native apps, but it is notoriously difficult to secure. Kubescape is the first open-source tool to test if Kubernetes is deployed securely according to multiple frameworks, including the MITRE ATT&CK framework and NSA-CISA guidelines.
It scans your clusters, YAML files, and Helm charts to find misconfigurations and software vulnerabilities. It even provides a “Risk Score,” so you can see at a glance how your security posture is improving over time.
Pacu: Exploitation framework for AWS penetration testing
To truly defend your cloud, you need to think like an attacker. Pacu is an open-source AWS exploitation framework designed for offensive security testing. It allows us to simulate real-world attack scenarios, such as T1078.004 (using compromised cloud accounts).
Pacu has modules for IAM abuse, privilege escalation, and data exfiltration. By running these simulations, we can find “attack paths” that automated scanners might miss. It’s the difference between checking if a door is locked and seeing if you can pick the lock.
Nikto: Web server and API security testing
Nikto is a classic web server scanner that is still incredibly relevant for testing cloud-hosted applications and APIs. It performs “black-box” testing, meaning it interacts with your running application just like an attacker would.
Nikto checks for over 7,000 potentially dangerous files, outdated server versions, and specific server misconfigurations. It’s a great tool for a quick “sanity check” on any web application you’ve just deployed to the cloud.
Best Practices for Implementing Cloud Security Testing Tools
Simply downloading these tools isn’t enough. You need a strategy to make them effective.
How to choose the right cloud security testing tools
When selecting your toolkit, keep these four factors in mind:
- Scalability: Can the tool handle your environment as it grows from 10 resources to 10,000?
- Multi-cloud Support: Since 89% of organizations use more than one cloud, your tools should ideally support AWS, Azure, and GCP.
- Integration Depth: Does the tool play nicely with your existing ticketing systems (like Jira) and communication tools (like Slack)?
- Automation Capabilities: In 2026, manual scanning is a recipe for disaster. Look for tools that can be fully automated.
Integrating security into DevSecOps workflows
The goal is to “Shift Left”—moving security testing as early in the development process as possible. By using pipeline integration, we can create automated “security gates.”
If a developer tries to deploy code that includes a critical vulnerability or an insecure configuration, the CI/CD pipeline can automatically block the deployment. This provides immediate feedback to the developer, allowing them to fix the issue before it ever reaches production. This is the core of an effective Infrastructure Vulnerability Assessment Tips Essential program.
Overcoming common pitfalls in cloud security assessments
Implementing these tools comes with challenges. The most common is alert fatigue. If your scanner sends you 500 alerts a day, you will eventually start ignoring them. To overcome this:
- Prioritize by Exploitability: Focus on the vulnerabilities that are actually reachable from the internet.
- Reduce False Positives: Use tools that provide “proof-of-exploit” to verify that a risk is real.
- Address Coverage Gaps: Ensure you aren’t just scanning your production environment; your dev and staging environments are often where attackers start.
- Manage Drift: Cloud environments change. Use tools that detect “configuration drift”—when someone manually changes a setting that was supposed to be managed by code.
Frequently Asked Questions about Cloud Security Testing Tools
What is the difference between CSPM, CWPP, and CIEM?
Think of it like securing a house. CSPM is checking if the windows and doors are locked (misconfigurations). CWPP is like having an alarm system inside the house (protecting the workloads/apps). CIEM is managing who has a key to the house and making sure they can only enter the rooms they need to (identity and permissions).
Which cloud security tools are best for AWS vs Azure vs GCP?
While many tools are multi-cloud, some have specific strengths. Prowler and Pacu are legendary for AWS. MicroBurst is a go-to for Azure penetration testing. For GCP, ScoutSuite and GCPBucketBrute are highly effective. However, for a general-purpose open-source stack, we recommend starting with Prowler and Trivy as they cover all three major providers well.
How do these tools help with compliance like NIST and HIPAA?
Most modern cloud security testing tools have built-in “compliance maps.” This means when the tool runs a scan, it doesn’t just tell you “this bucket is open”; it tells you “this bucket is open, which violates HIPAA section X and NIST control Y.” They automate the collection of evidence, making audits much faster and less painful.
Conclusion: Securing Your Cloud Future
The cloud landscape of 2026 is complex, but it doesn’t have to be scary. By leveraging these nine open-source cloud security testing tools, we can build a robust, automated defense that keeps pace with modern development.
At Aman Security, we believe that top-tier security should be accessible to everyone. We provide AI-powered automated penetration testing, SAST analysis, and real-time vulnerability scanning for your apps and infrastructure. Our tools are designed to be blazing-fast and comprehensive, offering free scans with instant AI explanations, fix suggestions, and professional reports.
Don’t wait for a breach to find out where your weaknesses are. Take control of your cloud security today. Visit Aman Security to start your journey toward a more secure cloud future. We’re here to help you navigate the complexities of cloud-native security with ease and confidence.
Secure Your Apps with Aman
Put these mitigation steps into practice. Get professional-grade vulnerability detection in one place.
Launch Your First Scan Now