How to Master Internal Network Penetration Testing Without Losing Your Mind
How to Master Internal Network Penetration Testing Without Losing Your Mind
Your Internal Network Is the Biggest Attack Surface You’re Not Testing
Internal network penetration testing is a controlled, hands-on security assessment that simulates what an attacker can do after they’re already inside your network — whether through a phished employee, a compromised device, or a malicious insider.
Here’s what it covers at a glance:
| What It Tests | Why It Matters |
|---|---|
| Lateral movement paths | Stops attackers from spreading across systems |
| Active Directory misconfigurations | Prevents full domain compromise |
| Privilege escalation routes | Limits damage from low-level access |
| Weak credentials and protocols | Closes doors attackers walk through daily |
| Network segmentation gaps | Contains breaches before they go wide |
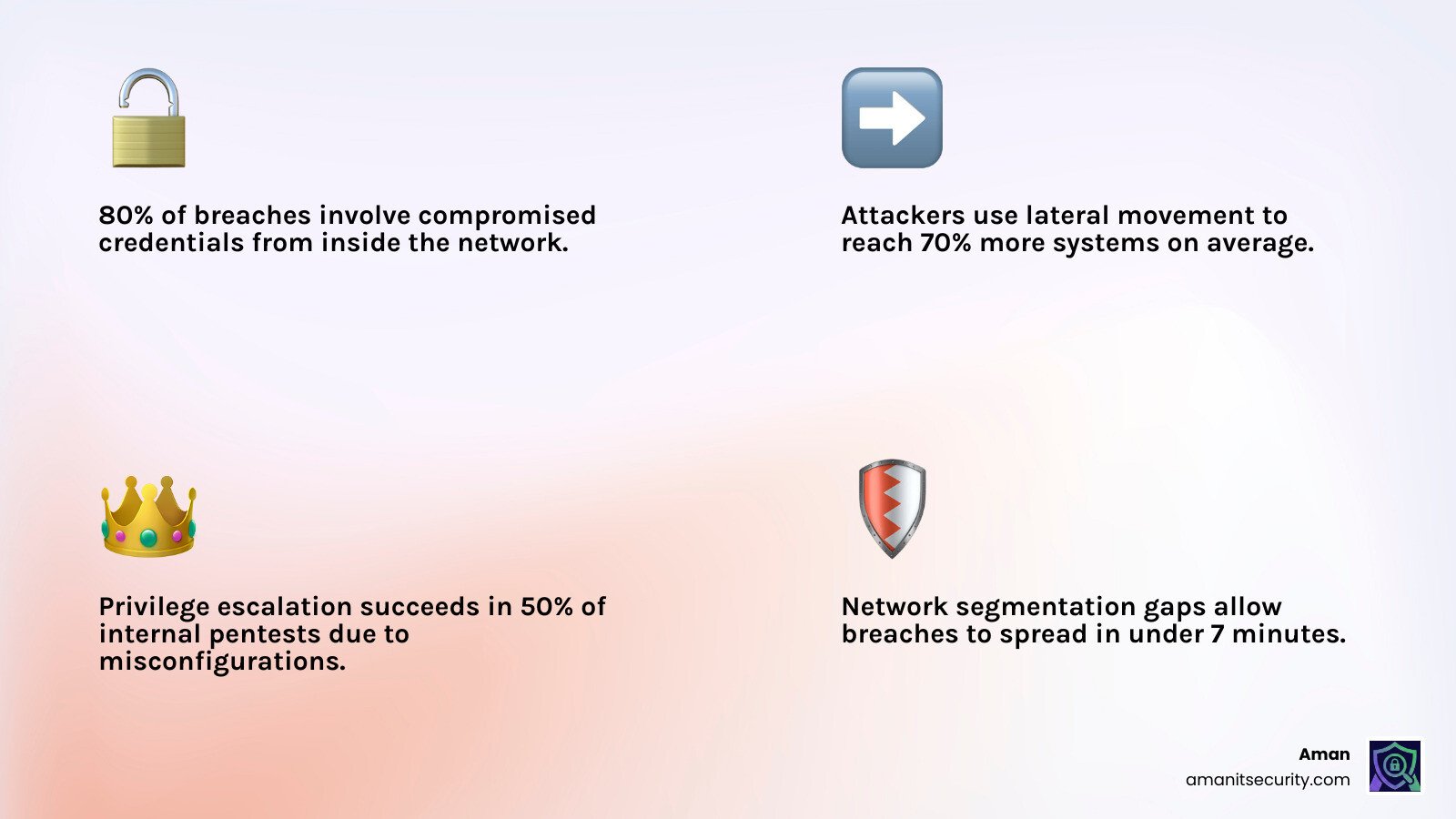
Most organizations spend heavily on firewalls and perimeter defenses. But the hard truth is that the majority of serious breaches start from inside — a phishing email lands, credentials get stolen, and suddenly an attacker is moving freely through your internal network.
The numbers are sobering. The average cost to remediate a ransomware attack more than doubled from around $761,000 in 2020 to $1.85 million in 2021. And in one of the most infamous cases, the NotPetya malware brought down a major global shipping company’s entire network in under seven minutes — spreading through internal Active Directory and lateral movement before anyone could respond.
Automated vulnerability scans won’t catch this. They flag known issues, but they don’t chain attacks, test real access paths, or show you what an attacker can actually reach once they’re inside.
That’s exactly what internal network penetration testing is designed to do.
I’m Zezo Hafez, an AWS and Azure certified IT professional with over 15 years of experience in cloud infrastructure and digital transformation — including hands-on work with the security architectures that internal network penetration testing is designed to stress-test. In this guide, I’ll walk you through everything you need to know, from methodology and tooling to remediation and compliance.
What is Internal Network Penetration Testing and Why Does It Matter?
At its core, an internal network penetration test is about assuming the breach has already happened. We aren’t looking at the front door; we’re looking at how someone could ransack the house once they’ve climbed through a basement window. It focuses on the vulnerabilities within your private network that an attacker could exploit to escalate privileges, steal data, or deploy ransomware.
When we perform these tests, we are emulating two main types of threats:
- The Malicious Insider: An employee or contractor with legitimate access who decides to go rogue.
- The Compromised Insider: An employee who accidentally clicks a link, giving an external attacker a “foothold” on their workstation.
The financial stakes are massive. For example, the ransomware attack costs for remediation doubled recently, hitting an average of $1.85 million. If you don’t test your internal defenses, you are essentially gambling that your perimeter is 100% impenetrable—a bet that history shows is a losing one.
Internal vs. External Penetration Testing
To understand why you need both, let’s look at how they differ:
| Feature | External Penetration Test | Internal Network Penetration Test |
|---|---|---|
| Starting Point | Outside the network (Internet) | Inside the network (LAN/VPN) |
| Primary Target | Web servers, Firewalls, VPN endpoints | Active Directory, File shares, Internal apps |
| Threat Model | Anonymous hacker, Script kiddies | Malicious employee, Compromised workstation |
| Goal | Gain initial access | Lateral movement and privilege escalation |
| Complexity | High (Hard to get in) | Very High (Hard to stop once they’re in) |
Internal Network Penetration Testing for Compliance
If you’re in a regulated industry, internal testing isn’t just a “nice to have”—it’s a “must-have.”
- PCI DSS: Requires internal network penetration tests annually for merchants and every six months for service providers. It also demands testing of network segmentation to ensure your “cardholder data environment” is actually isolated.
- SOC 2 & ISO 27001: While they don’t always use the exact phrase “internal pen test,” they require periodic risk assessments and validation of security controls. An internal test is the gold standard for proving those controls work.
At Aman Security, we believe that why AI-powered penetration testing is the new industry standard is largely due to these compliance burdens. AI can help you maintain “audit-ready” status 365 days a year, rather than just scrambling once a year before the auditors arrive.
Why Perimeter Defenses Are Not Enough
Think of your network like a castle. Firewalls and WAFs are the high walls and the moat. They are great at stopping the “noisy” attacks. But what happens if someone walks through the gate disguised as a merchant? Or if a guard is bribed?
Once an attacker has a foothold, they often find a “flat” network. This means once they are on one computer, they can see every other computer in the company. Common issues include:
- Phishing Footholds: Once an attacker controls one laptop, they can sniff network traffic or steal passwords from memory.
- Firewall Bypass: Many firewalls are “stateful,” meaning they block incoming traffic but allow outgoing traffic. Attackers use this to create “reverse shells” that bypass the firewall entirely.
- Zero Trust Gaps: Many organizations claim to have Zero Trust but still allow any internal device to talk to the Domain Controller.
For more on bridging this gap, check out The No-Nonsense Guide to Using AI for Penetration Testing Success.
The Standard Methodology: How an Internal Pen Test is Conducted
We don’t just “start hacking.” A professional internal network penetration testing engagement follows a strict, repeatable process to ensure nothing is missed and nothing is accidentally broken.
- Scoping: We define exactly what is being tested. Are we testing the whole office? Just the data center? The guest Wi-Fi?
- Rules of Engagement (RoE): This is the “law” of the test. It defines when we test (e.g., after hours for sensitive servers) and what techniques are off-limits.
- Information Gathering & Recon: We map the network. We look for open ports, active hosts, and naming conventions.
- Vulnerability Assessment: We use automated tools to find low-hanging fruit like unpatched Windows servers or old versions of Linux.
- Exploitation: This is where the “pen” in pen test happens. We try to use the vulnerabilities we found to gain access.
- Post-Exploitation: Once we have a “user” account, we try to become an “Admin.” Once we are an Admin on one machine, we try to become a “Domain Admin” (the keys to the kingdom).
- Reporting: We document every step. A good report includes an Executive Summary for the bosses and a technical breakdown for the IT team.
We often align our work with the PTES Methodology and NIST SP 800-115 Standards to ensure the highest level of rigor.
Common Scenarios in Internal Network Penetration Testing
To make the test realistic, we usually simulate one of these common “bad day” scenarios:
- The Rogue Device: We imagine an attacker walks into your lobby and plugs a small, malicious device (like a Raspberry Pi) into an open Ethernet port under a desk. Can that device reach your servers?
- The Low-Privileged User: We are given a standard set of employee credentials (no admin rights). We see if we can “escalate” those rights to see HR files or financial data.
- Guest Wi-Fi Pivoting: We sit in the parking lot on the Guest Wi-Fi and see if there are any “leaks” that allow us to jump onto the internal corporate network.
Modern testers often use tools like a Zero Trust Gateway to securely connect to your network for testing without needing a clunky VPN.
Preparation and Scoping Best Practices
Preparation is the difference between a helpful test and a stressful one. Here is our checklist for organizations:
- Identify Assets: Know what you have. You can’t test what you don’t know exists.
- Flag Sensitive Hosts: If you have a 20-year-old server running a critical database that crashes if you look at it funny, tell your testers!
- Verify Backups: Always have a fresh backup before a test starts. It’s the ultimate safety net.
- Schedule Wisely: Don’t run an internal pen test on the same day you’re doing a major software migration.
If your internal network relies heavily on APIs, you might also want to look at The Ultimate API Pentesting Tools Roundup to ensure your data interfaces are included in the scope.
Vulnerabilities and Tools: Breaking Down the Internal Attack Surface
The internal attack surface is a playground for hackers because internal systems are often less “hardened” than external ones.
The Active Directory (AD) Problem
In most companies, Active Directory is the brain of the network. If the brain is sick, the whole body is at risk.
- Active Directory Certificate Services (ADCS): Misconfigurations here are incredibly common and can allow an attacker to impersonate any user, including the CEO.
- Kerberoasting: This is a technique where we “request” a ticket for a service and then crack the password of that service account offline. It’s quiet and very effective.
- LLMNR/NBT-NS Poisoning: This is like “digital eavesdropping.” When a computer on your network asks “Where is the printer?”, an attacker can shout “I’m the printer! Give me your password!” and the computer often will.
The Pentester’s Toolkit
We use a mix of open-source and professional tools:
- Nmap: The “gold standard” for network mapping. It tells us what’s alive and what ports are open.
- Metasploit Framework: A massive library of exploits that helps us turn a vulnerability into an actual access point.
- Impacket: A collection of Python scripts that are essential for attacking Windows protocols and Active Directory.
Advanced Techniques for Internal Network Penetration Testing
Once we have a foothold, we don’t just sit there. We move.
- Lateral Movement: This is the act of jumping from one computer to another. Maybe we find a password stored in a text file on a developer’s desktop that works on a database server.
- Token Impersonation: We “steal” the login session of an administrator who recently logged into a machine we control.
- Pass-the-Hash: We don’t even need your password. If we have the “hash” (the scrambled version of the password), we can sometimes use that to log in directly.
The field is moving fast, and the best AI penetration testing tools for 2026 are already starting to automate these complex lateral movement paths.
Exploiting Misconfigurations and Weak Protocols
Sometimes, we don’t even need an “exploit.” We just use the way your network was built against it.
- SMB Signing Disabled: If this is off, we can perform “Relay” attacks, intercepting traffic and using it to run commands on other servers.
- Open File Shares: You would be shocked at how many “CompanySalaries.xlsx” or “NetworkPasswords.txt” files we find on shares that are open to “Everyone.”
- Cleartext Passwords: Many old applications send passwords over the network without encryption. We just “sniff” them out of the air.
For those running internal web portals, Web Applications Penetration Testing techniques are often used to find vulnerabilities like SQL Injection that can lead to a full database leak.
Real-World Risks and Remediation Best Practices
Let’s talk about the “NotPetya” elephant in the room. In 2017, the NotPetya case study became the ultimate cautionary tale for internal security. It used a combination of the “EternalBlue” exploit and credential theft (Mimikatz) to spread.
The shipping giant Maersk saw their entire global operation halt. They reported $300 million in losses. Their network was brought to its knees in just seven minutes. They were only able to recover because a single domain controller in their Nigerian office happened to be offline during a power outage, preserving a clean copy of their Active Directory. Internal network penetration testing is designed to find the exact paths NotPetya took before a virus does.
Handling Potential Issues During Testing
We know that “penetration testing” can sound scary to an IT Director. “Will you crash my servers?” is a common question.
- System Crashes: While rare with experienced testers, they can happen if a server is running very old, unpatched software. We mitigate this by discussing sensitive systems during the scoping phase.
- Existing Compromises: Sometimes, we start a test and find that a hacker is already there. If this happens, we stop immediately, notify you, and help you switch to “Incident Response” mode.
- Test Anxiety: It’s normal to be nervous! We recommend testing critical systems during maintenance windows or after hours to give you peace of mind.
To stay ahead of these risks, many are turning to Top Tools for Penetration Testing Using AI to Outsmart the Bots.
Post-Test Remediation and Retesting
A pen test report is only as good as the work you do after you get it.
- Prioritization: Don’t try to fix everything at once. Fix the “Critical” and “High” issues first—these are the ones that lead to Domain Admin access.
- Network Segmentation: This is the #1 fix. If your Accounting department’s computers can’t talk to the Warehouse’s computers, a virus in Accounting can’t spread to the Warehouse.
- Fix Verification: Once you think you’ve fixed an issue, have the testers try to exploit it again. This is called “retesting.”
- Continuous Monitoring: Security isn’t a one-time event. Modern teams use Generative AI Penetration Testing Prompt Engineering for Pentesters to create continuous testing loops.
Frequently Asked Questions about Internal Network Penetration Testing
How frequently should internal network penetration tests be conducted?
At a minimum, you should test annually. However, if you make significant changes to your infrastructure (like moving to the cloud or merging with another company), you should test again. For high-security environments, continuous validation is becoming the new norm.
Can an internal pen test crash my production servers?
It is very unlikely, but not impossible. Professional testers use “non-destructive” versions of exploits whenever possible. The risk of a crash during a pen test is much lower than the risk of a crash (and data wipe) during a real ransomware attack. Clear Rules of Engagement are your best protection here.
What is the difference between a vulnerability scan and a pen test?
A vulnerability scan is like an automated tool that checks if your doors are locked. An internal network penetration testing engagement is like a master locksmith trying to pick the lock, climb through the vent, and see if they can open the safe. Scans find potential problems; pen tests prove they are real and show the business impact.
Conclusion
Mastering internal network penetration testing doesn’t have to be a nightmare. It’s about moving from a “hope-based” security model to a “validation-based” one. By simulating the worst-case scenarios today, you prevent the headline-grabbing disasters of tomorrow.
At Aman Security, we make this process seamless. We provide AI-powered, automated penetration testing and vulnerability scanning that is blazing-fast and comprehensive. Our platform doesn’t just find the holes; it gives you instant AI-driven explanations and fix suggestions so your team can remediate in minutes, not months.
Ready to see what’s really happening inside your network? Secure your internal network today with a free scan and get professional-grade reports that keep the auditors happy and the hackers out.
Secure Your Apps with Aman
Put these mitigation steps into practice. Get professional-grade vulnerability detection in one place.
Launch Your First Scan Now